Network deployment and insights about proper techniques and procedure came at a great expense to us. We not only had to learn what college taught us, but also the rigid and tumultuous changes in the Windows/Linux world that happen right under our noses. The computer market is changing so fast that we have to hold on to our seats. There are many companies trying hard to make a buck and often at the expense of the consumer. What seems like a simple software install turns into an insidious attempt to market and advertise at the expense of keeping control of a machine’s processes. For Example, many printers and cameras come with non essential but required software that ends up infecting the system with spy-ware and advertising. Sadly a simple printer installed with default settings can add hundreds of useless megabytes of information on the computer that is purely harmful. Experience guides the qualified network administrator to make decisions about topology. More than just learning what to do… we have learned what not to do. We devote careful and planned attention to every last detail of a network that our company deploys. We will not rest unless every computer on every network is pristine and unhindered by unnecessary processes.
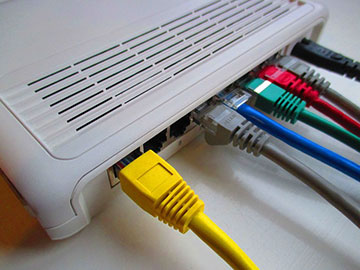
Here are some of the basic services we provide while putting together network infrastructure in Rochester NY, Philadelphia PA and Bucks County PA:
- Network Design
- Network Setup
- Network Service
- Careful Planning of Network
- Running Cable
- Installing Racks
- Wireless Setup
- Network Security
- Terminal Service
- VPN
- Redundant Backup on and offsite
Many of the things that make a good network admin are not apparent. Knowing what hardware and imaging tools to deploy and how to user them is one major component. Choosing the correct hardware for the job can be troublesome as well if it’s not planned accordingly. What is important to decide when choosing hardware is clear. The hardware needs to be fast enough to handle the Operating System and all its components and settings and it also has to be conducive with one of the leading imaging software programs. The process of organizing and separating Operating Environment from data is well defined and illustrated on the End The Virus Cycle blog. It is so crucial that every machine on a network, workstations and server alike, have imaging software installed and deployed. Imaging software allows for the “going back in time” phenomenon. As long as careful attention is made to imaging the computers environments when they are fully deployed and perfect, going back in time to that state anywhere on the network is minutes away. Newer tools of virtualization bring imaging concepts a step further. Virtualization helps to lighten the physical computer footprint on a network while doubling or tripling proficiency. Ask about this.
What is very important to our company is making sure that our clients understand the simple and useful tools that give them power and control. It is incredibly valuable to have a map with you on every road trip (in case your GPS fails). In a similar manner, it is incumbent that we leave our clients with knowledge of the tools we deliver for them. The true goal of our company is to provide help and support getting the client and their network exactly where they need to be, and then moreover making sure they have all the knowledge and keys to unlock the mysteries themselves. We truly enjoy educating at Fullyrealized, LLC. That is why we support such a wide scope of customers. There is just as much value and importance in deploying a home network as there is to deploy a large business network. Our mission is to help all sorts of people in all walks of life with the furthering and betterment of their computing and lives in general.
We deploy entire on premise systems. We take careful attention to detail and security concerns as well. Pfsense is one of the leading open source options for a secure front end gateway. The ability to control what comes in and out of a network is crucial. Our clients NEVER get violated from nefarious malware because we protect them at the gateway (router) level. We can sleep at night while seeing continuous stories in the media about various forms of ransom-ware and malware. It just does not happen when the proper systems are planned and deployed in a business environment. Tools such as Snort and IP/Continent restrictions prevent these types of vulnerabilities. When the computer attack vector is minimized/removed, the security of a set of systems can be relied upon.
In addition to the above mentioned ideas we also provide cable wiring services of all kinds to help facilitate a fast, strong and secure network.
We provide the following to customers upon request.
• Category 6
• Fiber
• Patch Panels
• Wireless & Wired Networks
• Connecting Multiple Locations & Offices
Please feel free to reach out to us and ask what we can do for your network/security needs.

